Fig. 2
From: Under false flag: using technical artifacts for cyber attack attribution
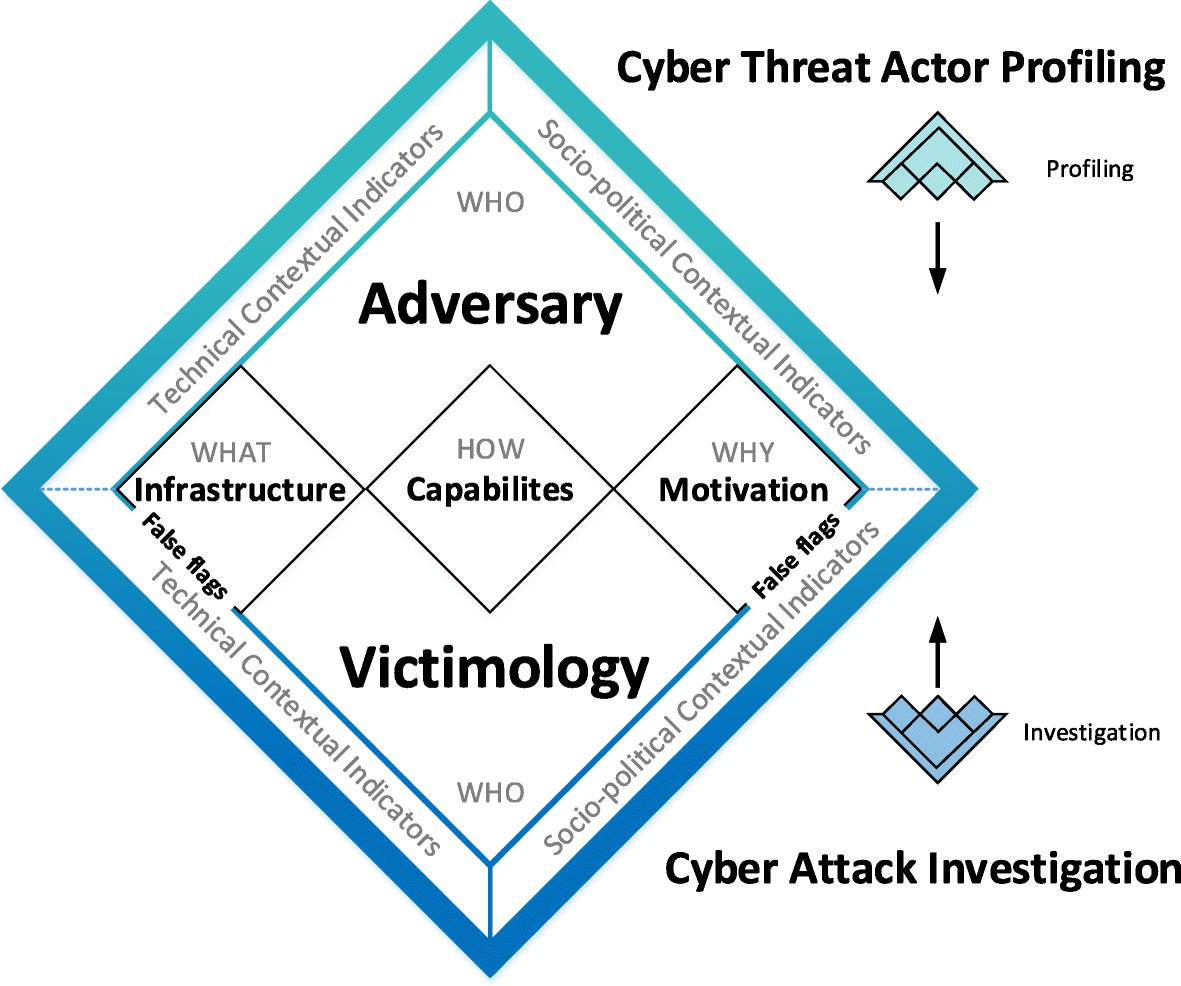
The Cyber Attribution Model applied to detect inconsistencies in the attribution process
From: Under false flag: using technical artifacts for cyber attack attribution
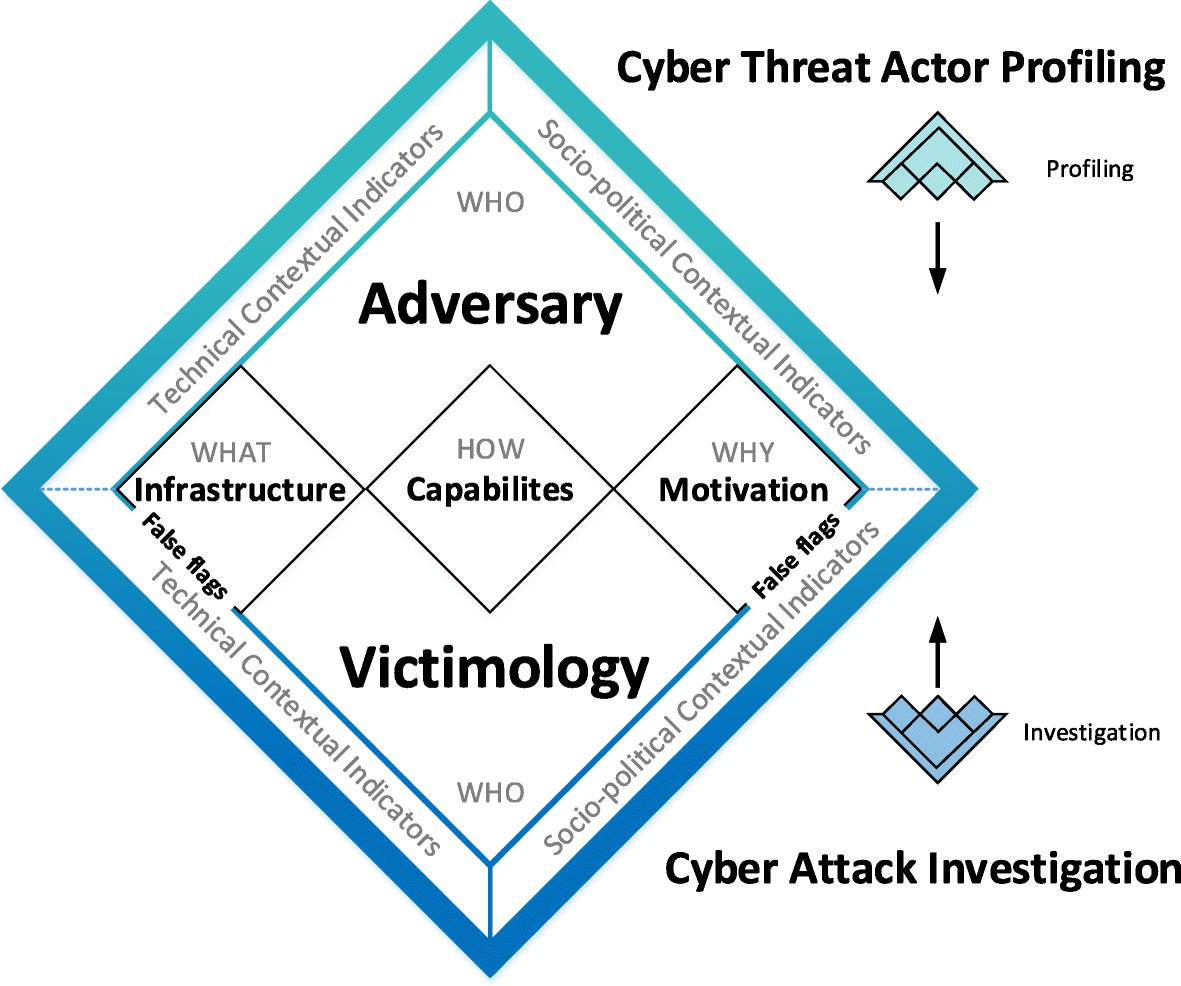
The Cyber Attribution Model applied to detect inconsistencies in the attribution process